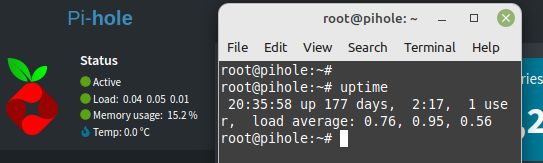
During a few of my AWS Cloud infrastructure build outs, client team members tend to wonder and ask why I use both Internet Gateway service, as well as a NAT Gateway service when setting up the network layer of the environment. Some with advanced networking knowledge made a point stating that we could skip the NAT configuration, and use the Internet Gateway service for all Internet access, which technically is true, and can be done. As a matter of fact, for smaller configurations with limited complexity requirements, that is a common practice; a single Internet Gateway service for all ingress/egress Internet traffic.
But why is that in other complex and large environments, especially where security is of a high concern, we tend to use different internet facing Gateway services? and what is the benefit of doing so?
Continue reading Cloud Connectivity in AWS: Choosing Between NAT and Internet Gateways